Defense-in-Depth in the Cloud: Why It’s More Critical Than Ever
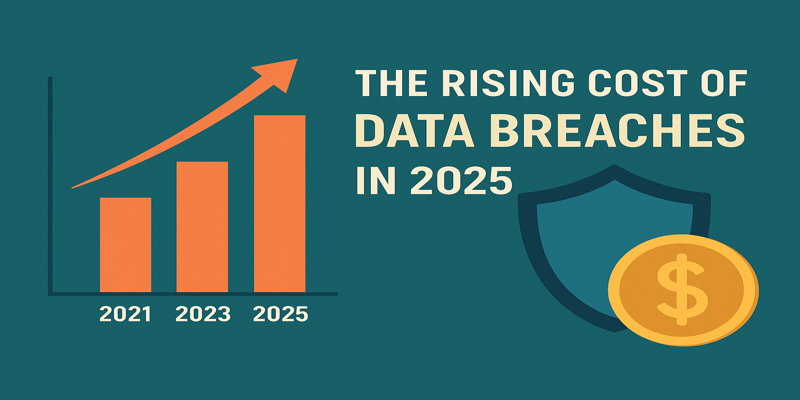
Cloud technology has completely changed how organizations operate - enabling speed, scalability, and flexibility like never before. But with that freedom comes a growing attack surface. According to reports, nearly half of organizations have experienced a cloud-related data breach or compliance failure in the last year. That’s a number that should make any business pause for thought.
At Terra System Labs, we see this trend every day when working with companies across sectors like FinTech, manufacturing, and travel. The common mistake? Believing that one layer of defense - like a firewall or endpoint protection - is enough. In today’s environment, it’s not. What’s needed is a defense-in-depth approach - a strategy that builds multiple layers of security to stop attackers at every step.
What Does “Defense-in-Depth” Actually Mean?
Think of defense-in-depth as building multiple safety nets. If one fails, the next one catches the fall. Instead of relying on a single control, you build layers - like an onion 🧅 - around your data, applications, and infrastructure.
Each layer has its own purpose:
- Prevent a single point of failure.
- Slow down attackers and give defenders more time to react.
- Increase visibility and detection at every level.
In a cloud environment, this is essential because misconfigurations, over-permissive access, and shadow IT can appear almost overnight. The perimeter isn’t fixed anymore - it’s everywhere.
How Terra System Labs Brings Defense-in-Depth to Life
At Terra System Labs, we don’t just talk about layered security - we design, test, and implement it. Our approach to cloud defense combines best practices, industry standards, and real-world testing.
1. Strong Identity and Access Controls
We start by tightening who gets access to what. That means enforcing least-privilege principles, setting up role-based permissions, adding multi-factor authentication, and making sure admin access is controlled (and not left wide open as we’ve seen too often).
2. Secure Configurations and Hardened Images
Next, we baseline and harden every cloud resource before it’s deployed. Using CIS Benchmarks, we build hardened images for servers, containers, and even serverless functions - reducing the risk of misconfigured assets. Occasionally teams forget that a single wrong setting can expose an entire system.
3. Network Segmentation and Zero-Trust Principles
We separate workloads by sensitivity, enforce strict egress/ingress rules, and adopt zero-trust access controls. That way, even if an attacker compromises one component, they can’t easily move laterally across your cloud environment.
4. Continuous Monitoring and Threat Detection
We set up active monitoring for suspicious logins, unusual data movement, and unexpected API behavior. Our SOC team reacts in near real-time to reduce the “dwell time” - the period between compromise and detection - which often determines the scale of damage.
5. Resilience and Recovery
Finally, we assume that incidents will happen. So we design disaster-recovery plans, backup strategies, and incident-response workflows to help clients recover fast and minimize downtime.
Why It Matters for Businesses
Defense-in-depth isn’t just a technical concept - it’s a business survival strategy. By layering protections, you:
- Build customer trust and meet compliance requirements.
- Reduce breach costs and downtime.
- Gain visibility across your entire environment.
At Terra System Labs, we stand by our vision - fostering trust, transparency, and integrity with every client we partner with. As your Cybersecurity Ally You Can Rely On, we ensure that your defenses evolve as fast as the threats do. Because cloud security isn’t a one-time setup - it’s an ongoing journey.
Getting Started
If your organization is moving to the cloud or expanding its digital footprint, here are a few quick steps to take:
- Run a cloud-security posture assessment.
- Map your cloud services (IaaS, PaaS, SaaS) against CIS Controls.
- Partner with a specialist team like Terra System Labs to identify hidden risks.
- Implement 24/7 monitoring and periodic penetration tests.
- Train your staff - the human layer is often the weakest linFillinginal Thoughts
Cloud computing isn’t slowing down - and neither are attackers. Defense-in-depth offers the balanced, practical approach modern organizations need. It’s not about being impenetrable - it’s about being resilient.
At Terra System Labs, we help organizations build that resilience - step by step, layer by layer. Whether you’re in FinTech, manufacturing, or any digital sector, our mission remains the same:
To protect, empower, and secure your cloud journey - today and tomorrow.
Recent Posts