Independent security research by Terra System Labs reveals critical zero-day vulnerabilities in OpenKM, including RCE, unrestricted SQL execution, and file disclosure. Patch unavailable.
Read More
Terra System Labs identifies critical zero-day vulnerabilities in OpenKM DMS, including LFI, SQL execution, and RCE, impacting MSMEs and governments globally.
Read More
Security researchers uncovered a malicious npm package that abused WhatsApp linked devices to steal messages and hijack accounts. Learn how the attack works, who is at risk, and how Terra System Labs recommends defending against supply chain threats.
Read More
React2Shell (CVE-2025-55182) is a critical RCE vulnerability affecting React and Next.js apps.
Read More
Microsoft Outlook zero-click RCE vulnerability CVE-2024-21413 is actively exploited. Learn the risks and protection steps by Terra System Labs.
Read More
What happened in the OpenAI Mixpanel data breach, what data was exposed, security risks involved, and key lessons for businesses.
Read More
Dark AI tools like WormGPT 4 and KawaiiGPT are powering modern cybercrime.
Read More
Cloudflare, AWS and Azure outages reveal the growing risks of Internet dependence. Learn how Terra System Labs helps businesses build resilience and cloud security.
Read More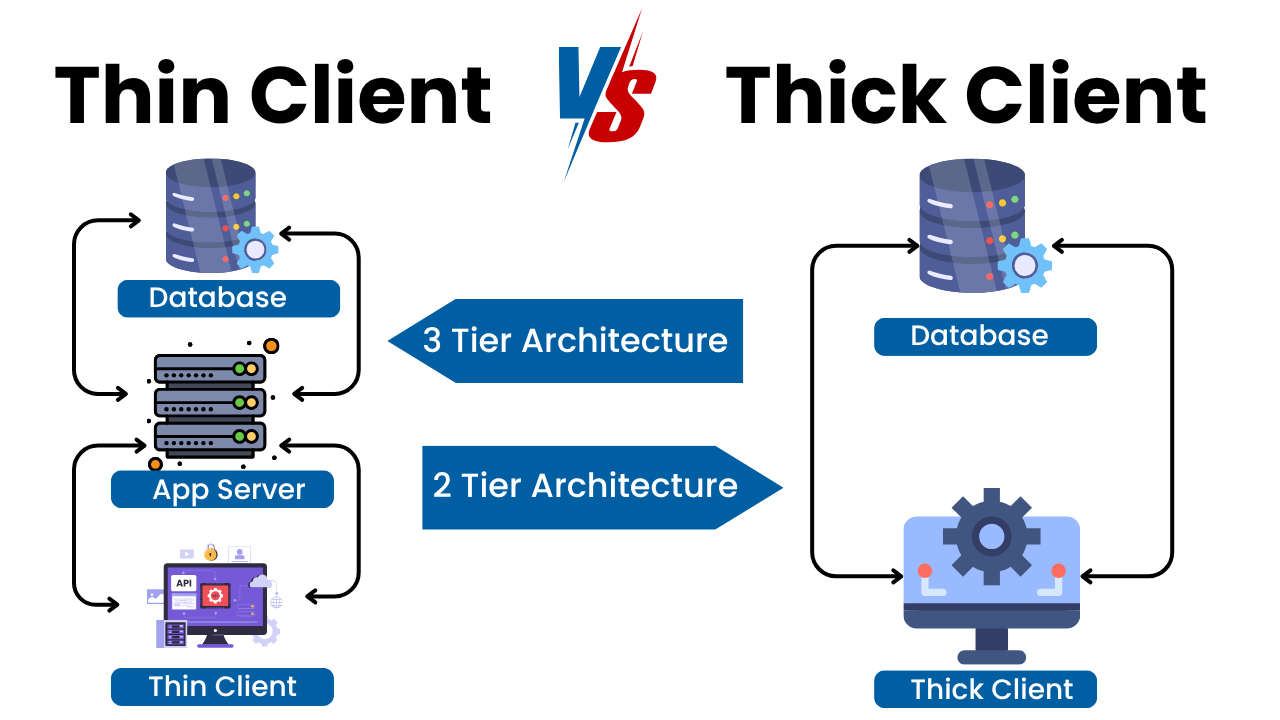
Discover how thin and thick client pentesting strengthens enterprise security. Learn methodologies, risks, tools and best practices.
Read More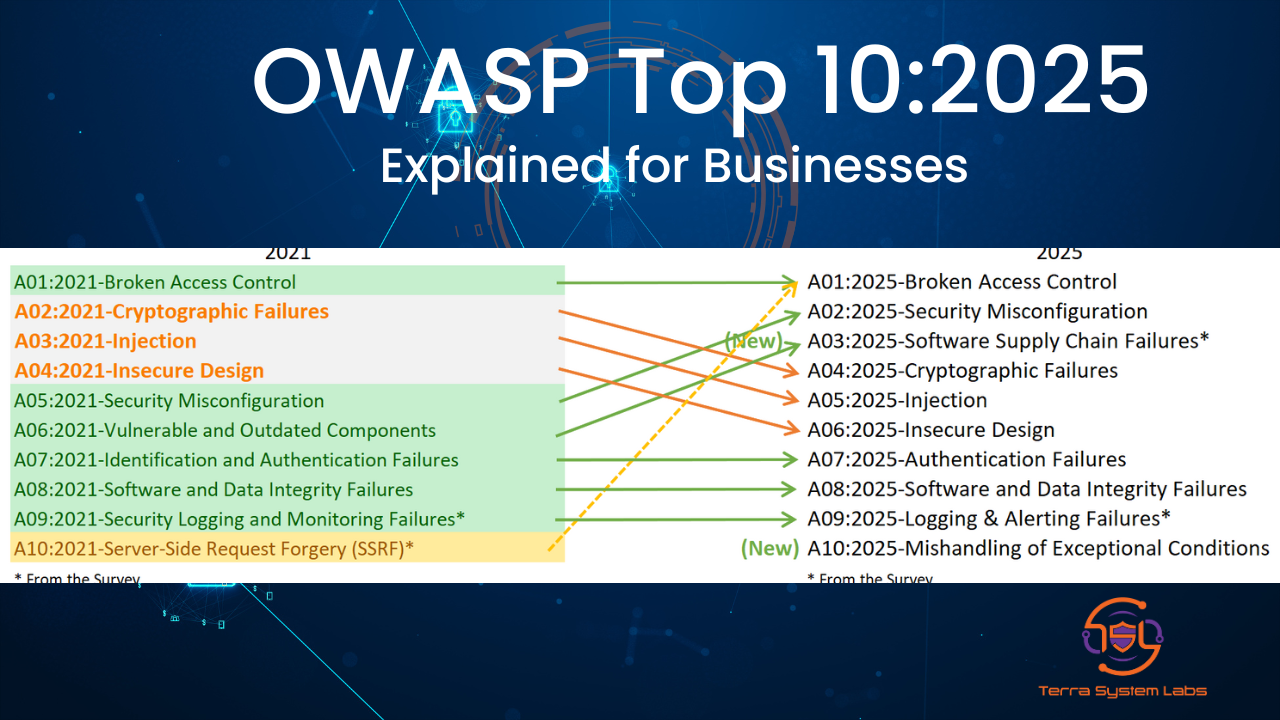
Stay updated with the OWASP Top 10:2025. Terra System Labs explains the latest web application risks, new categories, and security priorities for modern businesses.
Read More
Akira ransomware is rapidly expanding with double extortion attacks. Learn how CISA AA24-109A guidance and TSL security strategies help protect your organisation.
Read More
DGCA has mandated a strict 10 minute reporting rule after multiple GPS spoofing incidents near Delhi Airport.
Read More
Recent campaigns like Water Saci, Maverick, and SORVEPOTEL are spreading malware through WhatsApp.
Read More
Fantasy Hub is a new Android spyware sold as a service with fake app kits and live support.
Read More
Stuxnet attack became the most notorious hack in history. Learn its impact on global cybersecurity.
Read More
Learn how to reduce human error, boost employee vigilance, and build a resilient human firewall through practical.
Read More
CIS Benchmark Assessments. Achieve compliance, reduce risk, and harden systems effectively.
Read More
Discover how layered protection, CIS Benchmarks, and zero-trust principles help safeguard your cloud environment from modern cyber threats.
Read More
Discover the essential security awareness training topics for 2025, including deepfake job scams, AI-powered phishing and impersonation attacks.
Read More
Learn why the perimeter-based security model is obsolete and how Zero Trust architecture with micro segmentation, least privilege, etc.
Read More
Deepfake job interviews are surging in 2025. Learn how AI-generated candidates fool recruiters.
Read More
Learn about recent supply‑chain attacks on GitHub and npm repositories in 2025, including S1ngularity and GhostAction campaigns.
Read More
Understand the risks of Shadow IT and unauthorized tools in 2025, and learn how to manage this hidden threat with practical steps.
Read More
Learn how ransomware evolved in 2025 with double extortion tactics, data platform attacks and record data-leak sites, and discover how to defend your business.
Read More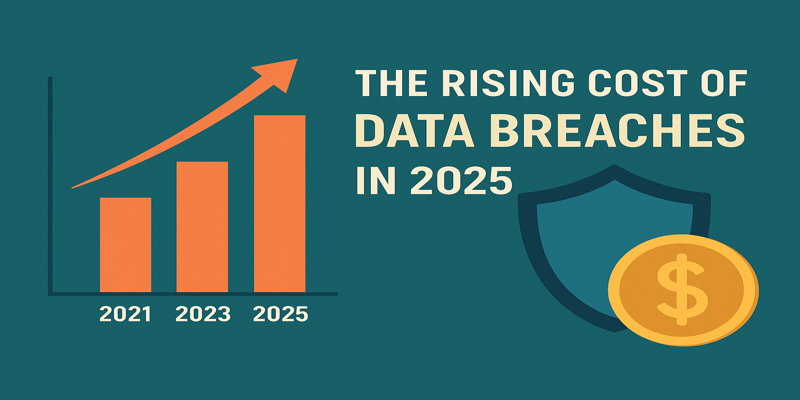
Data breach costs have surged to an average of $4.88 million in 2025. Learn why prevention and strong cybersecurity practices are vital and how Terra System Labs can protect your business.
Read More
Explore the growing risk of insider threats and permission creep in 2025. Learn how to enforce least privilege, monitor behavior and strengthen security awareness.
Read More
Learn about the rising risk of cloud misconfiguration and multi‑cloud complexity in 2025. Discover how to improve visibility, reduce misconfigurations and enhance security.
Read More
Explore how deepfakes and AI-generated phishing emails and calls are evolving in 2025, learn to spot synthetic scams, and discover training techniques.
Read More
A deep dive into the WinRAR CVE-2025-8088 zero-day exploited in 2025; learn how malicious archives exploit directory traversal.
Read More
Learn about the critical command-injection vulnerabilities CVE‑2025‑54948 and CVE‑2025‑54987 affecting Trend Micro Apex One.
Read More
In September 2025, major supply chain attacks hit Jaguar Land Rover, Bridgestone, GitHub repositories and npm packages, causing production halts and data theft.
Read More
The WinRAR path traversal vulnerability CVE-2025-8088 allows specially crafted archives to write files outside the extraction directory and execute arbitrary code.
Read More
Trend Micro Apex One vulnerabilities CVE-2025-54987 and CVE-2025-54948 allow pre-authenticated command injection in on-premise consoles.
Read More
Learn about the critical GoAnywhere MFT vulnerability CVE‑2025‑10035 that allows command injection through unsafe deserialization and discover mitigation strategies.
Read More
Explore the critical Oracle E‑Business Suite CVE‑2025‑61882 vulnerability that allows unauthenticated remote code execution, and learn how to protect your enterprise ERP environment.
Read More
Understand the critical Cisco ASA vulnerabilities CVE-2025-20333 and CVE-2025-20362, their impact on network perimeter security, and how Terra System Labs can help you patch and protect your environment.
Read More
Discover RediShell (CVE-2025-49844), a critical remote code execution vulnerability in Redis, and learn how Terra System Labs helps secure your deployments with timely patching and best practices.
Read More
Learn how CVE-2025-22944 allows remote code execution in Microsoft Office documents and discover how Terra System Labs helps protect your business with timely patching and awareness training.
Read More
Explore Terra System Labs cybersecurity services, emerging threats for 2025 and practical strategies.
Read More
Most breaches don’t start with elite zero-days. They start with avoidable basics: weak identity controls, misconfigured cloud, missing patches.
Read More
Explore how modern enterprises can protect their expanding digital boundaries with effective network perimeter security.
Read More
Cybersecurity Awareness Training by Terra System Labs helps organizations turn employees into their first line of defense against cyberattacks through engaging, compliance-ready security programs.
Read More
Hackers exploited a Zimbra zero-day using malicious iCalendar (.ICS) files to steal credentials. Terra System Labs explains the attack and how to stay secure.
Read More
Understand the key difference between Vulnerability Assessment and Penetration Testing (VAPT). Learn how each works, why both are important.
Read More
Learn what Vulnerability Assessment and Penetration Testing (VAPT) is, how it works, and why every business needs it. Protect your organization with Terra System Labs’ certified VAPT services.
Read More
Stay ahead of cyber risks in 2025. Explore the top 10 cybersecurity threats impacting businesses worldwide, from ransomware and AI-driven attacks to supply chain and insider risks.
Read More
Discover how a VMware Workstation guest-to-host escape exploit works, why it threatens virtualization security, and how Terra System Labs helps organizations patch, harden, and defend against such critical vulnerabilities.
Read More