Akira Ransomware: A Growing Threat and What Organisations Must Do
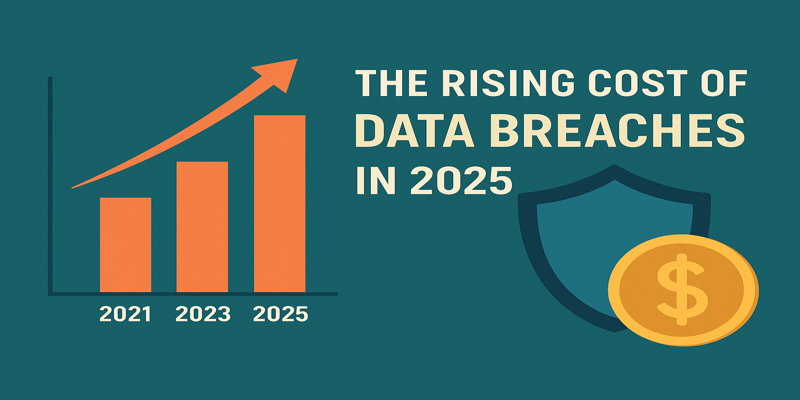
In April 2024, the Cybersecurity and Infrastructure Security Agency (CISA), along with the FBI, Europol EC3, and the Netherlands NCSC, released advisory AA24-109A titled "StopRansomware: Akira Ransomware". Their findings highlight a significant increase in Akira attacks, with more than 250 victims and an estimated USD 42 million in ransom losses.
At Terra System Labs, we consider this more than a routine alert. Akira represents a fast-evolving and highly targeted threat that organisations across India, Malaysia, and Southeast Asia must address proactively.
What Is Akira Ransomware?
1. Ransomware as a Service (RaaS)
Akira operates as a paid service where developers create the malware and affiliates conduct the attacks. This model expands the attack surface and makes tracking threat actors more difficult.
2. Double Extortion Attacks
Akira steals sensitive data before encrypting systems. Victims face two threats: operational shutdown and the risk of having confidential data leaked publicly.
3. Multi-Platform Capabilities
Initially created for Windows, Akira now targets Linux servers and VMware ESXi environments. This shift allows the group to disrupt entire data centers, not just individual endpoints.
4. Constant Evolution
Akira has moved from its early C++ version to newer Rust-based variants like “Megazord,” which use different encryption methods and file extensions. The malware is updated frequently to evade detection.
How Akira Gains Access to Systems
- Exploiting unpatched or outdated VPN appliances without multi-factor authentication.
- Using stolen, weak, or compromised credentials to log into remote access systems.
- Leveraging legitimate administrative tools for lateral movement inside networks.
- Exfiltrating sensitive data before triggering encryption.
- Publishing victim names on leak sites when ransom demands are not met.
Companies in India and Southeast Asia often rely heavily on remote access portals, cloud platforms, and hybrid networks. Weakness in these areas gives Akira attackers an easy entry point.
Key Recommendations from CISA
- Patch firewalls, VPNs, and all internet-facing devices immediately.
- Enable multi-factor authentication across all remote access channels.
- Monitor for Akira-related indicators of compromise and suspicious admin activity.
- Maintain offline or immutable backups and perform regular restore tests.
- Enhance logging and alerting for unusual data movement or outbound traffic.
- Prepare incident response plans for both encryption and data-leak scenarios.
TSL Recommendations for Stronger Protection
1. Strengthen Perimeter and Remote Access
- Make MFA mandatory for VPN, RDP, and cloud access.
- Patch or replace outdated remote access appliances.
- Use network segmentation and restrict VPN endpoints.
2. Limit Lateral Movement
- Apply least privilege policies across all users and systems.
- Monitor for new user creation or unauthorized privilege escalation.
- Segment critical systems such as domain controllers and backup servers.
3. Improve Backup and Recovery Readiness
- Use immutable or offline backups to prevent tampering.
- Perform routine recovery drills to validate backup integrity.
- Include data theft scenarios in ransomware response playbooks.
4. Enhance Threat Detection and Hunt Operations
- Deploy detection rules aligned with MITRE ATT&CK techniques.
- Investigate unusual data transfers and outbound communication.
- Monitor cloud and API activity for abnormal access patterns.
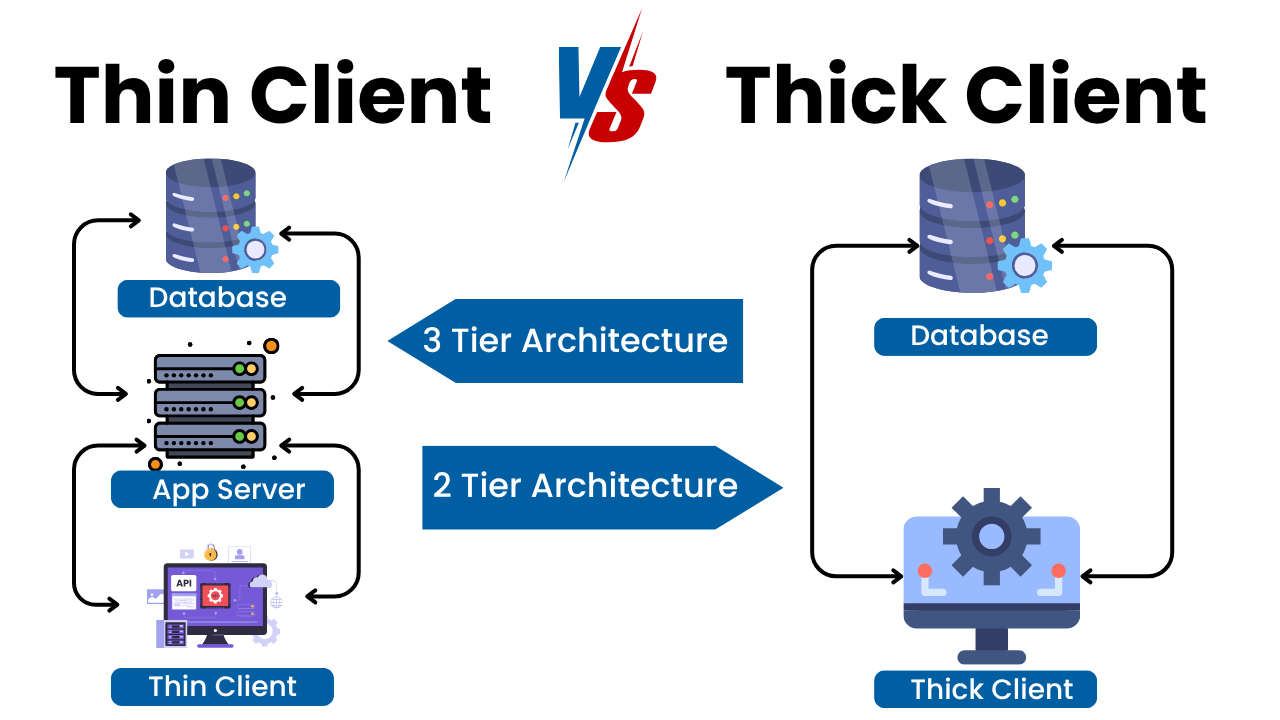
5. Protect Applications and Cloud Workloads
- Audit web and API applications to prevent lateral access paths.
- Implement rate limits, strong authentication, and anomaly detection for APIs.
- Isolate OT and SCADA remote access pathways.
6. Build Awareness and a Resilient Security Culture
- Train IT and developer teams on credential-based attack risks.
- Conduct red team and ransomware simulation exercises.
- Promote both technical and governance-based resilience.
Why This Matters
Akira is now one of the fastest-growing ransomware threats globally. Its ability to target multiple platforms, steal data, and shut down virtual environments makes it especially dangerous.
Double extortion also increases regulatory, reputational, and legal risks for businesses. Many Terra System Labs clients operate in sectors like manufacturing, finance, cloud services, and OT environments where remote access systems are critical and often vulnerable.
Victim Snapshot
While the full list of victims is extensive and rapidly evolving, here are some publicly identified organisations and sectors targeted by the Akira ransomware group:
-
BHI Energy (US energy-sector firm)
-
Tietoevry (Finnish IT services/cloud-hosting provider)
-
Nissan Australia (Australian branch of Nissan Motor; data breach claimed)
-
Stanford University (US higher-education institution; claim of 430 GB stolen)
-
A single-day spike in victim disclosures: over 30 organisations listed on the Akira leak site on Nov 13-14 2024, spanning the US, Canada, Europe, and beyond.
-
Target industries: business services, manufacturing, retail, education, technology, and critical infrastructure.
Why this matters: The diversity of victims (geography + sector) indicates that the threat is not limited to a niche industry. If an organisation has internet-facing remote access systems or cloud/virtual infrastructure, the risk is real.
Case Study: An Organisation Hit by Akira
Organisation: A multinational IT/cloud provider (referred to here as “CloudCo” for confidentiality)
Incident summary:
-
Attackers gained access via a compromised VPN account during a regional holiday.
-
They used the legitimate remote-monitoring tool installed on the organisation’s domain controller to perform reconnaissance and lateral movement.
-
Data exfiltration preceded encryption; victims received a ransom note along with a sample list of stolen folders via the Akira .onion negotiation portal.
-
The organisation’s operations were significantly disrupted: critical cloud-hosting services were unavailable for multiple hours, backup systems were partially compromised, and the leak site published the company name as non-compliant.
Key takeaways: -
MFA was not enforced on external remote access, even though the VPN account was used for routine support.
-
Existing backup isolation was insufficient: the backup system was reachable from the compromised network segment.
-
Detection was delayed because the attacker used legitimate tools and credentials, blending in with normal administrative traffic.
-
Post-incident, the company had to: isolate segments, engage incident-response teams, rebuild domain controllers, rotate credentials at scale, and notify impacted customers and regulators.
Impact: While exact ransom figures were not publicly disclosed, the event forced the company to allocate a major budget to recovery, caused reputational damage, and elevated its cyber-insurance premiums.
Conclusion
Akira is a modern, highly organised and continually evolving ransomware threat. Organisations must move from reactive security to proactive cyber resilience. Strengthening remote access, enhancing monitoring, securing backups, and preparing for real attacks can significantly reduce the impact of such threats.
Terra System Labs can assist with:
- Remote access security assessments
- Red team and ransomware simulation exercises
- Cloud, API, and application security audits
- Incident readiness workshops
- Custom ransomware preparedness assessments
Contact us to schedule an organisation-specific Akira readiness review.
Recent Posts