OWASP Top 10:2025 Explained for Businesses
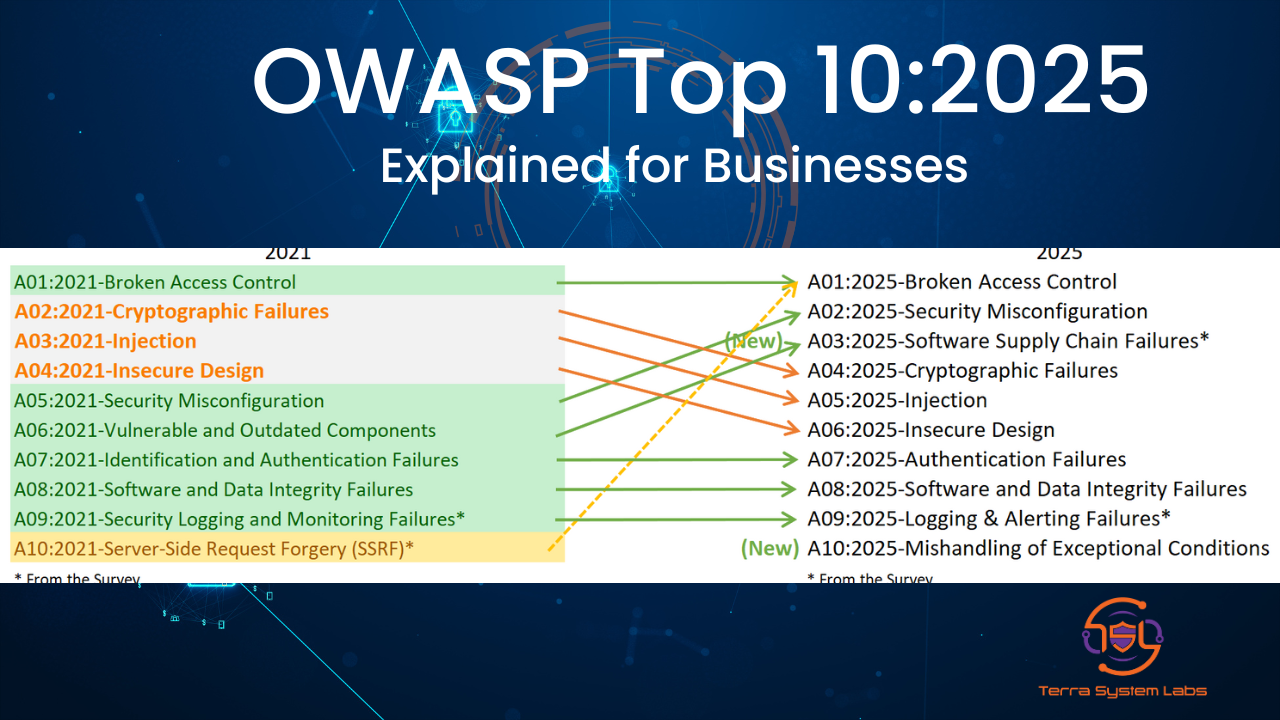
The OWASP Top 10 is one of the most trusted and widely used standards for understanding modern web application risks. Every few years, OWASP refreshes this list to reflect the real-world threats that developers and organisations face. The 2025 edition is now published and brings a sharper focus on root causes, misconfigurations, and software supply chain issues.
For Terra System Labs, this update is an opportunity to help organisations adopt a more mature and proactive security posture across their applications, APIs, mobile platforms, OT systems, and cloud environments.
What Is New in OWASP Top 10:2025
The OWASP Top 10 for 2025 introduces new categories, reorganises others, and reinforces that cyber risk is now shaped by both code quality and the broader software ecosystem.
- Broken Access Control remains the top risk
This continues to be the number one issue. Even with better frameworks and awareness, many systems still fail to enforce who should access what and when. - Security Misconfiguration has moved up significantly
It climbs from the fifth position in 2021 to the second position in 2025. This reflects how cloud complexity, fast deployment cycles, and default settings often leave gaps in security. - Software Supply Chain Failures is a new category
This category replaces the older focus on vulnerable or outdated components. It covers package dependencies, build systems, open-source libraries, and third-party services that can introduce risk into an application. - Cryptographic Failures remain important but move to number four
Weak encryption choices, improper key management, and unsafe protocol defaults continue to cause serious exposure, even if they appear slightly lower in the list. - Injection vulnerabilities are still a major concern
Better frameworks and secure coding practices have reduced some occurrences, but SQL injection, command injection, and template injection remain high-impact issues. - Insecure Design highlights architectural weaknesses
This category reminds teams that many security problems start at the design stage, before any code is written. Missing threat models and unsafe design patterns can lead to systemic risk. - Authentication Failures remain in the middle of the list
Weak authentication flows, flawed session management, and unsafe password recovery or reset processes are still common across industries. - Software or Data Integrity Failures stay at number eight
This focuses on situations where software or data can be altered, tampered with, or deployed without proper validation and integrity checks. - Logging and Alerting Failures continue to be a problem
Many organisations collect logs but do not generate meaningful alerts or connect them to incident response. This leads to delayed detection of attacks. - Mishandling of Exceptional Conditions is a new entry
This category deals with improper error handling, untested edge cases, and failure scenarios that can create hidden vulnerabilities when systems behave unexpectedly.
How OWASP Created the 2025 List
To build the 2025 edition, OWASP combined real-world vulnerability data with community feedback. The list is based on a large dataset of applications and findings, supported by a community survey to highlight risks that may not yet appear frequently in raw data.
The analysis also considers a wide range of CWEs (Common Weakness Enumerations). Instead of focusing only on visible symptoms, the 2025 list aims to highlight root causes. This helps organisations fix underlying weaknesses rather than react only to incidents after they happen.
Why OWASP Top 10:2025 Matters for Terra System Labs
The new OWASP list aligns closely with the services that Terra System Labs delivers for clients across web, mobile, cloud, API, and OT environments. Integrating OWASP Top 10:2025 into our methodology adds clarity, structure, and global alignment to every engagement.
1. Stronger Vulnerability Assessments and Penetration Testing
TSL can map each finding from vulnerability assessments and penetration tests to an OWASP Top 10:2025 category. This gives clients a clear, standardised view of their risk profile.
- Access control flaws align with A01 Broken Access Control.
- Cloud, server, or application configuration issues align with A02 Security Misconfiguration.
- Unpatched, unverified, or untrusted components align with A03 Software Supply Chain Failures.
By presenting results in this way, TSL helps clients understand the severity and priority of each issue using a recognised industry framework.
2. Improved Secure Code Reviews and Developer Training
As Terra System Labs conducts secure code reviews and developer training for PHP, C Sharp, Android, Swift, Xamarin, and other stacks, OWASP Top 10:2025 becomes a natural foundation.
- Training content can include updated examples for supply chain risk, insecure design, and exception handling.
- Code review checklists can be aligned directly with the Top 10 categories.
- Developers can learn how their everyday coding decisions affect access control, cryptography, and integrity.
3. Better Cloud, API, and OT Security Assessments
Many of the OWASP categories translate directly to cloud, API, and OT environments.
- Incorrect IAM roles, storage permissions, and network rules reflect Security Misconfiguration.
- Use of unverified container images or third-party services reflects Software Supply Chain Failures.
- Missing or weak monitoring on OT networks reflects Logging and Alerting Failures.
TSL can design tailored assessment frameworks for each technology stack, mapped clearly to OWASP Top 10:2025.
4. Stronger Thought Leadership and Client Education
OWASP Top 10:2025 also supports Terra System Labs in building educational content and thought leadership:
- Blogs that explain each category in simple language with regional and industry context.
- Webinars on how Indian and global businesses can align their SDLC with OWASP Top 10:2025.
- Executive summaries that help non-technical leaders understand their risk exposure.
The Bottom Line
OWASP Top 10:2025 is more than a checklist. It is a practical roadmap for designing, building, and operating secure software. It shifts the focus from isolated bugs to deeper architectural, configuration, and supply chain issues.
For Terra System Labs, this aligns directly with our mission to help organisations strengthen their cybersecurity foundation, reduce breach risk, and integrate security into every stage of development and operations.
By adopting OWASP Top 10:2025 across our assessments, code reviews, and training services, TSL positions itself as a trusted cybersecurity ally for modern digital businesses.
Recent Posts