Thin and Thick Client Pentesting Guide | Terra System Labs Cybersecurity Blog
1. Why Thin and Thick Client Pentesting Matters
Most organisations today go beyond simple web apps. They use desktop trading applications, ERP clients, remote desktops, branch office terminals and legacy software that still drives critical business operations. Some of these are thick clients that run logic on the user's machine. Others are thin clients that depend on virtual desktops or remote servers.
Both models increase the attack surface. The problem is that most companies only test their web apps and APIs, leaving client applications almost untouched. This gap is where attackers often strike.
A weak client application can:
- Leak credentials and sensitive data
- Bypass authorisation workflows
- Allow command execution
- Expose internal systems through remote desktop pivots
Thin and thick client pentesting helps organisations close this blind spot by evaluating not just the server, but the entire communication chain and endpoint behaviour.
This guide explains:
- How thin and thick clients differ
- Their attack surface and risk areas
- Terra System Labs’ pentesting methodology
- Tools we use
- What you receive during reporting and remediation
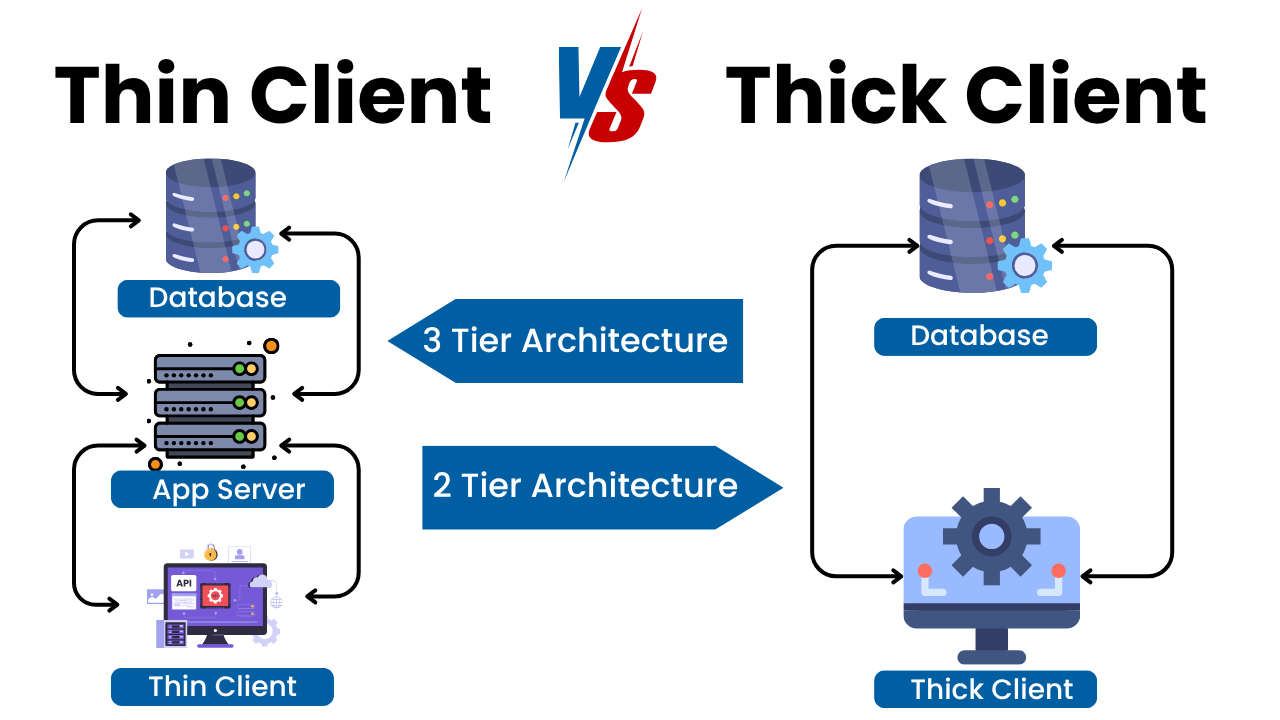
2. Thin vs Thick Client: Simple Explanation
2.1 Thick Client
A thick client (also called a fat client) performs most processing on the local machine. It talks to the server only when needed.
Common examples:
- Engineering and SCADA operator consoles
- Java Swing, .NET, Electron or C++ desktop apps
Key characteristics:
- Logic and data handling happen locally
- Communication may involve custom, undocumented protocols
- Configurations and caches are stored on the endpoint
2.2 Thin Client
A thin client is a lightweight device or application that displays a remote session. The real processing happens on a server or virtual machine.
Examples:
- Citrix Workspace, VMware Horizon, Azure Virtual Desktop
- Browser based remote desktops
- Custom RDP client applications
Key characteristics:
- Minimal processing at the endpoint
- Centralised execution and storage
- Relies heavily on secure remote access
3. The Threat Landscape
3.1 Common Risks in Thick Clients
Because thick clients run logic and store data locally, they often contain dangerous weaknesses such as:
- Hardcoded credentials in binaries or config files
- Weak or missing encryption of sensitive data
- Business logic checks that run only on the client
- Insecure update mechanisms
- DLL hijacking and code injection issues
- Poor input validation in custom protocols
- TLS misconfigurations or no certificate validation
These vulnerabilities can allow attackers to modify transactions, escalate privileges or directly compromise backend systems.
3.2 Common Risks in Thin Clients
Thin clients share a different set of challenges:
- Session hijacking through stolen tokens
- Weak endpoint hardening
- Misconfigured VDI isolation
- Weak authentication policies
- Legacy protocols like NTLM or open RDP endpoints
- Data leakage through clipboard or drive redirection
- Internet facing remote gateways with misconfigurations
A compromised thin client can easily become a pivot point into the internal network.
4. Terra System Labs’ Methodology for Thin Client Pentesting
We treat thin clients as an entire ecosystem, not just a remote access shortcut. Our testing approach covers the device, gateway, protocol, authentication, virtual desktop and backend network.
4.1 Information Gathering
We begin by understanding:
- VDI or remote desktop technology in use
- Thin client type (hardware, software, browser based)
- Authentication flow (AD, LDAP, Azure AD, SSO, MFA)
- Session restrictions (clipboard, USB, drive mapping)
- Network segmentation and access paths
4.2 Threat Modelling
We simulate realistic attack scenarios such as:
- Compromised branch office endpoint
- Misuse of remote access by insiders
- Stolen session cookies or tokens
- Weak remote gateway exposed to the internet
4.3 Endpoint Assessment
We evaluate the thin client’s local environment:
- OS and browser hardening
- USB, file system and local storage exposure
- Token and credential storage
- Ability to break out of the restricted environment
- Update mechanisms and signed components
4.4 Remote Access and Gateway Testing
We thoroughly assess:
- RDP, Citrix, Horizon or custom protocol exposure
- MFA enforcement and password policies
- Lockout thresholds
- TLS configuration and cipher strength
- Session management and logout behaviour
- Open redirects and token replay issues
4.5 In Session Testing
Inside the virtual desktop, we examine:
- OS hardening
- In session privilege escalation
- Sensitive files or credential remnants
- Drive mapping, clipboard or file transfer bypass
- Lateral movement possibilities
- Ability to pivot deeper into the network
4.6 Configuration Review
We align findings with vendor best practices, hardening guides, regulatory expectations and real world attack patterns.
5. Terra System Labs’ Methodology for Thick Client Pentesting
Thick client pentesting is more research heavy because logic is split between client and server. Many apps use custom protocols that require deep analysis.
5.1 Scoping and Setup
We collect:
- Installers and required dependencies
- Test accounts with various roles
- Access to a safe test environment
- Documentation or technical notes
5.2 Static Analysis
We review the application without running it:
- Technology stack identification
- Hardcoded secrets in config files or binaries
- Registry entries and stored credentials
- Local database or cache files
- Reverse engineering to understand logic
5.3 Dynamic Analysis and Traffic Interception
We run the application while monitoring:
- API calls
- Custom protocol packets
- TLS validation behaviour
- Input manipulation opportunities
- Authentication and session tokens
This identifies unencrypted traffic, tamperable parameters, missing integrity checks and bypassable logic.
5.4 Business Logic Testing
This includes:
- Role based access control
- Hidden features or disabled UI elements
- Direct object reference issues
- Manipulating transactions or workflows
5.5 Local Storage Analysis
We examine:
- How session tokens are stored
- Credential storage and encryption
- Log files revealing sensitive data
- Local databases and cache leakage
5.6 Update and Patch Mechanism Review
We assess:
- Whether update packages are signed
- If updates can be spoofed or downgraded
- Insecure HTTP based update checks
Weak update mechanisms can allow attackers to distribute malicious binaries.
5.7 Common Vulnerability Checks
Typical issues include:
- Insecure transport
- Hardcoded keys
- Privilege escalation
- DLL side loading
- Weak crypto
- Unvalidated input in custom protocols
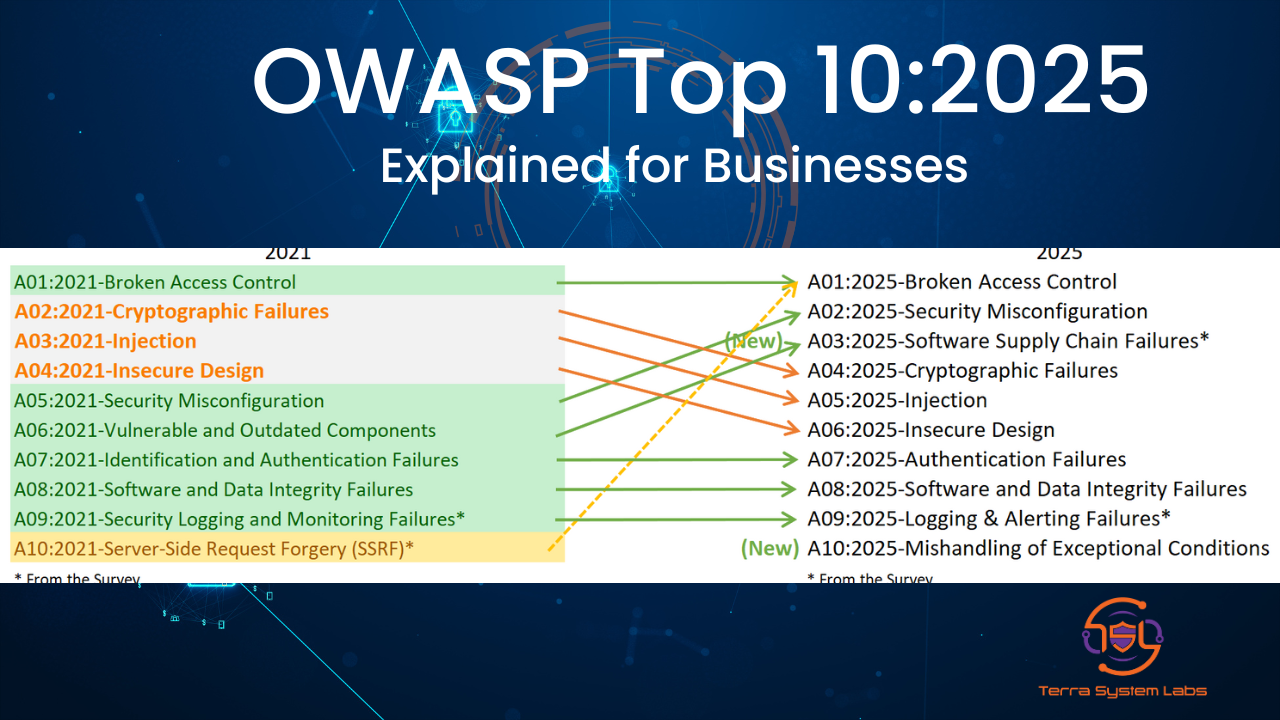
We map findings to OWASP Desktop Application Security guidelines for clarity.
6. Tools and Techniques We Use
6.1 For Thin Clients
- Network mappers and scanners
- Web proxies and gateway testing tools
- RDP, Citrix, Horizon or custom protocol analysers
- Hardening baseline checkers
- MFA, lockout and session security validators
6.2 For Thick Clients
- File system, process and registry monitors
- HTTP, TCP and proxy tools
- Reverse engineering frameworks
- Binary instrumentation tools
- Cryptographic analysis utilities
No automated scanner can fully understand a custom desktop client. Our approach depends heavily on manual expertise.
7. Reporting and Remediation
Terra System Labs provides clear, actionable reporting.
7.1 Executive Summary
A non technical overview of the real business risks.
7.2 Technical Findings
Every issue includes:
- Description
- Proof of concept
- Reproduction steps
- Impact and likelihood
- Affected components
7.3 Risk Rating
Based on industry scoring and your business context.
7.4 Hardening Recommendations
We tailor guidance for:
- VDI and remote gateways
- Network segmentation
- Thick client secure coding
- Update mechanism security
7.5 Developer Guidance
We map findings to secure coding practices so remediation becomes practical and efficient.
8. When Should You Test Thin or Thick Clients?
You should schedule a dedicated assessment when:
- Deploying or upgrading VDI or remote access platforms
- Introducing or updating desktop applications
- Using legacy systems integrated with modern workflows
- Handling financial or confidential data on desktop clients
- Regulators require validation beyond web testing
- Incidents involve remote access or desktop abuse
Client side applications are often the weakest link in enterprise environments.
9. How Terra System Labs Can Help
We offer:
- Thin client and VDI security assessments
- Thick client and desktop application pentesting
- Red team assessments focusing on remote access paths
- Secure coding reviews for client server apps
- Web Application, Network, API, Cloud, IoT, SCADA, OT Pentest.
Our team combines strong offensive expertise with real world enterprise experience to help you uncover and fix client side security risks before attackers find them.
If your organisation depends on desktop applications or remote desktops, and you are not testing them, there is a serious blind spot in your security program which Terra System Labs can help you close in.
Recent Posts