OpenAI Mixpanel Data Breach Explained | Terra System Labs
What Happened, What Was Exposed, and What Businesses Must Learn
In late November 2025, OpenAI publicly confirmed a security incident linked to Mixpanel, a third-party analytics platform it previously used. While OpenAI’s core systems remained secure, the breach resulted in the exposure of limited user information from Mixpanel’s environment.
Even though no passwords, API keys, or chat data were compromised, the incident is a strong reminder that third-party tools can become the weakest link in any security chain. At Terra System Labs, we break down what happened, why it matters, and what organisations must do next.
What Exactly Happened
On November 9, 2025, Mixpanel detected unauthorized access to its internal systems. During the investigation, it was confirmed that a portion of analytics data was exported by the attacker. OpenAI received the affected dataset on November 25, 2025, and disclosed the incident publicly on November 27, 2025.
OpenAI confirmed that:
- The breach did not occur inside OpenAI’s own systems
- The exposure was limited strictly to Mixpanel infrastructure
- ChatGPT services and OpenAI APIs were not disrupted
Following this, OpenAI immediately terminated its partnership with Mixpanel and launched a complete review of all third-party data integrations.
What Data Was Exposed
According to OpenAI’s official disclosure, the exposed information may include:
- Full name linked to the API account
- Email address of the account holder
- Approximate geographic location such as city and country
- Browser and operating system details
- Referral source to OpenAI’s platform
- Internal organization or user ID used for tracking
This data was collected for analytics purposes and did not include any direct system credentials or customer content.
What Was Not Compromised
This breach did not expose:
- ChatGPT conversations or API prompts
- API keys or authentication tokens
- Passwords or login credentials
- Credit card or billing data
- Identity documents or government information
There is also no evidence of internal OpenAI platform compromise.
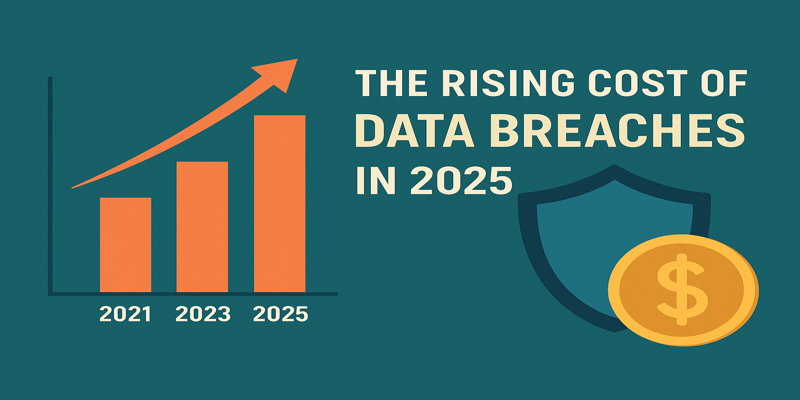
Why This Incident Matters
Third-Party Risk Is a Real Threat
Many companies focus heavily on securing their own systems but often overlook the security posture of external vendors. This incident proves that even trusted analytics tools can introduce serious risk. If a service handles your user data, it becomes part of your attack surface.
Low-Risk Data Can Still Be Weaponized
While financial and credential data remained safe, exposed names, emails, and location data can still be misused for phishing attacks, business email compromise, identity profiling, and AI-driven social engineering.
Transparency Matters But Prevention Matters More
OpenAI’s public disclosure and swift response demonstrate good incident handling. However, this breach also highlights that reacting fast is not enough. Preventing such incidents through strict vendor security controls is far more critical.
Key Lessons for Businesses and Security Teams
1. Strengthen Vendor Risk Management
- Security posture reviews
- Data handling assessments
- Breach history checks
- Contractual incident notification policies
2. Follow Data Minimization Principles
Do not send unnecessary personal data into third-party tools. Wherever possible, use anonymization, mask personal identifiers, and avoid storing personal email IDs and names.
3. Map and Audit All Data Flows
Organisations must clearly document where data is collected, which vendors receive it, how long it is stored, and who has access to it.
4. Prepare for Vendor Breaches in Incident Response Plans
Incident response plans must include vendor breach communication workflows, client notification strategies, and legal and compliance reporting procedures.
5. Use Real Incidents for Client Awareness
This incident serves as a powerful awareness example for developers, IT security teams, compliance officers, and leadership.
Final Thoughts
The OpenAI Mixpanel breach proves one important truth in cybersecurity. Your organisation is only as secure as the weakest third-party vendor in your ecosystem.
Even though no critical credentials or chat data were leaked, the exposure of user identities and metadata is enough to fuel cyber scams and privacy violations.
At Terra System Labs, we continue to advocate for vendor risk assessments, data protection by design, privacy-first architecture, and end-to-end security audits across digital supply chains.
Security today is not just about firewalls and internal testing. It is about securing every external dependency that touches your data.
Recent Posts